Skype, Microsoft’s now ubiquitous video/messenger program, has long been a go-to destination for attackers looking to peddle their malware.
The latest campaign to leverage the software – a botnet circulating adware, composed entirely of Skype users – was recently disrupted by researchers.
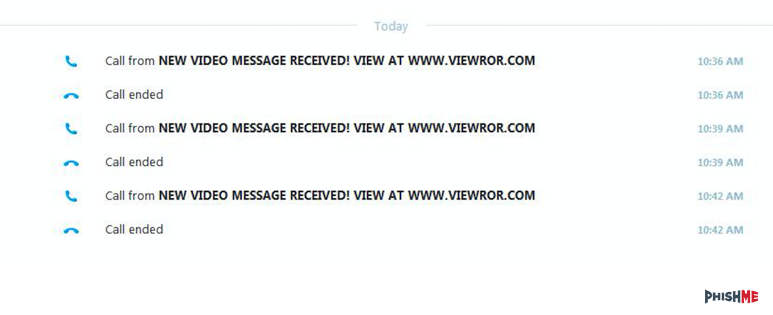
Ronnie Tokazowski, a senior researcher with the firm PhishMe, first knew something suspicious was afoot after he spotted an attacker sending call request after call request through the software.
The username instructs victims to go to a domain which if opened, prompts the user to download and install an executable: videoplayer.exe. The .exe promises it will install a video player to view content on the site. Once opened, the file does install a video player but also – inevitably – a slew of adware on the victim’s machine.
According to Tokazowski, who penned a blog entry about the disruption on Wednesday, in addition to the adware, each time a victim downloads it an affiliate program was likely generating money for the attacker on a per-install or per-download basis.
Tokazowski claims PhishMe worked alongside the security team from Amazon Web Services, who were unknowingly helping host some of the domains connected to the campaign, to help dismantle it. After gathering a list of domains and bot names the attackers used, they also forwarded them along to Microsoft, who helped with the takedown.
In January a handful of Skype users claimed they were seeing malicious ads that wound up leading them to sites that tricked them into downloading bogus Adobe and Java updates. Users unfamiliar with what Adobe or Java’s updates usually look like were duped by the fake ads.
Provided from: Techcrunch.