Some strains of Bartalex malware, a macro-based malware that first surfaced earlier this year, have recently been spotted dropping Pony loader malware and the Dyre banking Trojan.
Primarily spread through spam, the first iterations of Bartalex were observed in late March embedded in Microsoft Word and Excel macros.
Macros have been a popular infection method for a decade-plus but as is often the case in malware, everything old eventually becomes new again. The attack vector never really went away but Word documents booby-trapped with macro malware have been enjoying a comeback of sorts as of late. Microsoft’s Malware Protection Center even sounded the alarm over an increasing number of threats using macros in January.
Brad Duncan, a security researcher at Rackspace and handler at the SANS Internet Storm Center spotted Bartalex propagating through a rigged Word document on Tuesday.
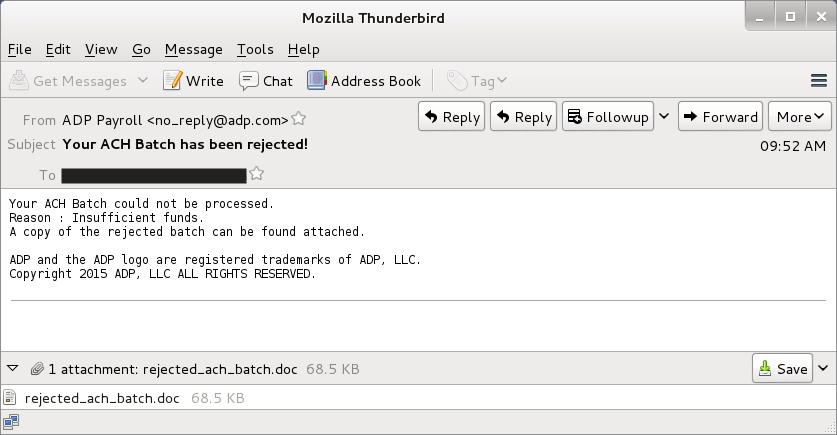
The Word document purports to come from the payroll service ADP and pertain to a rejected Automated Clearing House (ACH) payment. As Duncan notes, a quick look at the email’s header however indicates the email did not come from ADP and if a user were to open the file, assuming they have macros enabled in Microsoft Word, they’d execute any associated macros.
According to Duncan, who used network protocol analyzing tools to review traffic from the malware’s infection, there were some signs that Pony and Dyre were being deployed by this version of Bartalex. Using Wireshark Duncan noticed “certificate data typically seen in SSL traffic generated by Dyre” in the code and in Security Onion he spotted a “number of events related to Bartalex and the Pony downloader.”
The Pony Trojan, which been around for years, is known for stealing Bitcoin, passwords and other credentials but perhaps is most infamous for its role as a downloader. The Trojan commonly downloads other malware, often Gameover Zeus, onto machines it infects.
While Bartalex has been observed doling out Dyre before, this appears to be the first time Pony has been used to do so.
Researchers noticed attackers distributing Bartalex via thousands of malicious Dropbox links back in April of this year. The malware went on to download variants of Dyre, the banking malware that specifically targets user account credentials, onto machines it infected. Dropbox was quick to respond however and citing its Acceptable Use Policy, revoked the ability for the accounts involved with the campaign to share links.
Provided from: Techcrunch.